Four Tips To Help Keep Your Apis Safe
Jun 04, 2020 • 7 views
Most security breaches now involve APIs that help power apps and platforms. APIs make our lives easier by giving businesses a way to share data.
Most security breaches today involve APIs that help power apps and platforms. APIs help make our lives more simple by giving companies, like Lyft and Uber, an easy way to share data and info with each other.
APIs help gives you the experience you want and needs as a customer, giving you the tools to connect an app to your bank account, find the location of nearby drivers, bring up your profile, identify your own location and find the best route. Online services and mobile apps that ask you to input your credit card number, are the most prone to being impacted by API abuse. The most common API abuse involves abuse of the business logic of the application, including verifying email addresses, gift cards, and credit card numbers.
Some predict that by 2022, API abuse will be the most common attack that security teams see. And one study found that by 2021, 90 percent of web-enabled applications would have more surface area for attack for exposed APIs rather than the user interface. And with different APIs sending and receiving important data and information, there is always a risk to API security.
Many of the largest global companies manage hundreds of APIs and rely on much smaller third-party businesses to provide critical roles for their online business. Security breaches are often caused by APIs being accessed and abused by malicious actors.
Luckily, there are a few steps your business can take to protect your API:
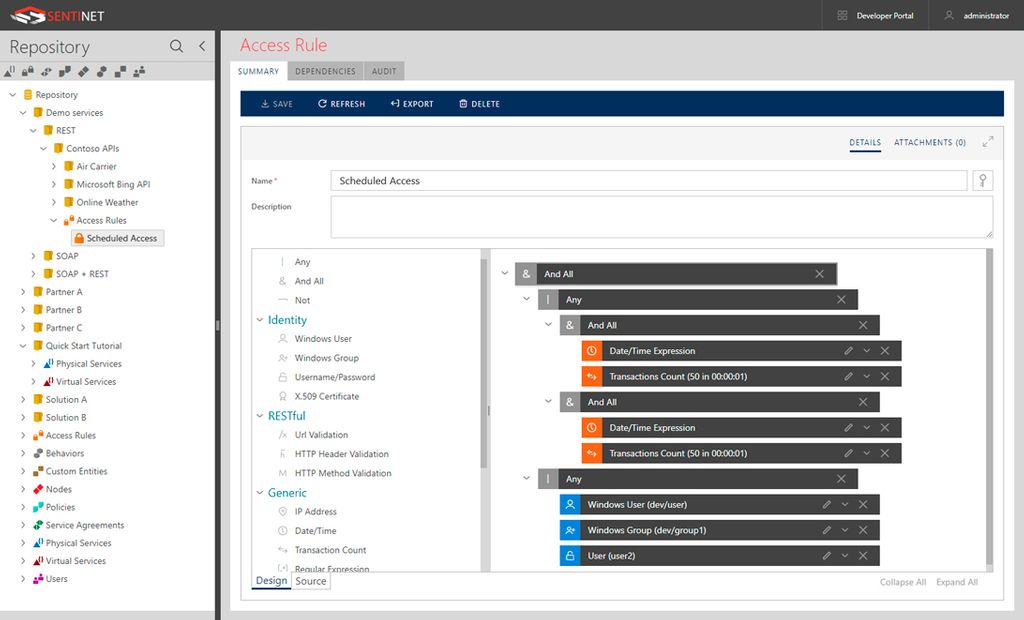
Manage authentications-One of the biggest ways to protect your API is to manage your authentications and make sure you know exactly who has access to what and what their permissions are. Cybercriminals often steal entire databases of emails and passwords in order to attack APIs with requests. Many cybercriminals are also attacking the APIs that power many mobile apps. Companies should use strict multifactor authentication in order to better protect their APIs from cybercriminals.
Check authorizations-Many larger companies manage hundreds of different APIs, and it can be super tricky to keep track of who is authorized to access or use certain data or information. Companies should definitely be wary of how their information is accessed and used with APIs. It can be difficult to detect API attacks, since cybercriminal requests are difficult to differentiate from regular requests. That’s why it’s so important to have a firm grasp on who has authorization in order to protect your API.
Organize security team setup-It’s crucial for your security teams to be set up in an organized manner that involves the entire company. Security teams used to be focused mainly on the infrastructure or network layer and steered away from the applications. But today, it is super important for the security team’s projects to be visible to the entire company.
Scrutinize third parties- Companies can be at risk of security breaches or API attacks even if they do all the right things. If even just one malicious actor third party service has access to your system, it could lead to a widespread security breach. Companies should therefore thoroughly vet their third-party parties before giving them access to their data.
